OUR SECURITY
Security is in everything we do
Discover why organizations trust us to successfully fend off security threats, denial of service attacks, and malicious software intrusions while providing data protection and meeting global compliance standards

Your trustworthy partner for data security and compliance
AuthenticID is committed to upholding strong information security policies and data privacy practices throughout all aspects of our business operations. We’ve completed data security and risk management certifications to attest our commitment and provide trust to our clients.

Intensely vetted personnel
Every AuthenticID staff member is required to go through extensive background checks, and regular security training. Security Awareness Training includes obligations related to information classification and handling, password security, virus protection, email hoaxes, desktop security, information security and social engineering.
Continuous vetting and training are pursued to maintain operational security while keeping developers in line with secure coding practices.
The Marks of Excellence
A comprehensive suite of deliverables to support your business needs
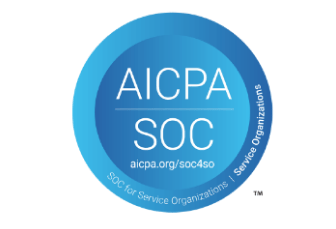
AuthenticID has achieved SOC2 certification to assure that critical service commitments and system requirements are in place to manage and protect client data.

Our ISO/IEC 27001 certification shows that AuthenticID meets the highest international standards for risk management by implementing, maintaining, and continually improving its information security management systems.

To ensure GDPR compliance, AuthenticID’s privacy policy identifies how personal data is collected, used , and stored. If you partner with AuthenticID we will support your GDPR compliance through ongoing efforts and will evolve our capabilities with the ever-changing regulatory landscape.
Enhancements for the most comprehensive identity solution
To minimize risk, access to production services and customer data is limited via controlled interfaces within specifically trained roles and responsibilities of AuthenticID personnel. Customer environment PII access is tightly controlled, monitored and audited both digitally and physically.
All data is encrypted in every AuthenticID use case. Our secure network connections are encrypted with TLS v1.2 or higher for application API communication, user web portal access, system maintenance and logging platforms. AES-256 and RSA-2048 are used to provide trusted encryption methods.
Strict NIST-driven password policies and multi-factor authentication methods (MFA) are required for all production services and system access. User permission segregation, hierarchy, and unique credentials are required for all PII access to achieve full customer environment data separation at all times.
AuthenticID incorporates governance and change-management traits into the core functions of our engineering discipline. To ensure that customers experience consistent and repeatable operations, we practice peer code reviews, conduct regular code audits, implement change control, and facilitate unit testing, system integration testing, and penetration testing.
Access AuthenticID’s Trust Package
The AuthenticID Trust Package is a curated library showcasing key components of our Information Security Compliance Program. Designed for professionals in Compliance, Procurement, and Vendor Management, the Trust Package provides a real-time, centralized view into our security and compliance practices.
This resource offers transparency into how AuthenticID manages its compliance controls and security frameworks, supporting your due diligence and third-party risk management efforts.