Everything you need to manage identity-based transactions with confidence.
AuthenticID’s Identity Proofing and fraud deterrence solutions use proprietary, 100% automated machine learning and computer vision technologies to ensure that people are who they claim to be. Our portfolio of products offers a complete fraud prevention solution to meet any business’s KYC and IAM requirements.
Identity Proofing.
The complete fraud solution bundle.
Identity Proofing is a comprehensive offering that combines our verification and fraud detection products into a complete KYC and IAM package. Now all businesses can instantly verify the identities of their customers and employees with the highest accuracy to prevent fraud.
- Ideal for account openings and onboarding
- New employee enrollment
- Re-authentication & step-up authentication
ID Verification.
With our 100% automated proprietary Identity Proofing solution, you can catch even the most sophisticated fraudulent documents and professional fraudsters. In addition to detecting fraudulent IDs, our image capture technology gives you the ability to capture and process low-quality images with the most challenging backgrounds and lighting. What’s more, our proprietary OCR, 2D barcode and MRZ data extraction technology has the highest accuracy in the industry and supports over 30 international languages.

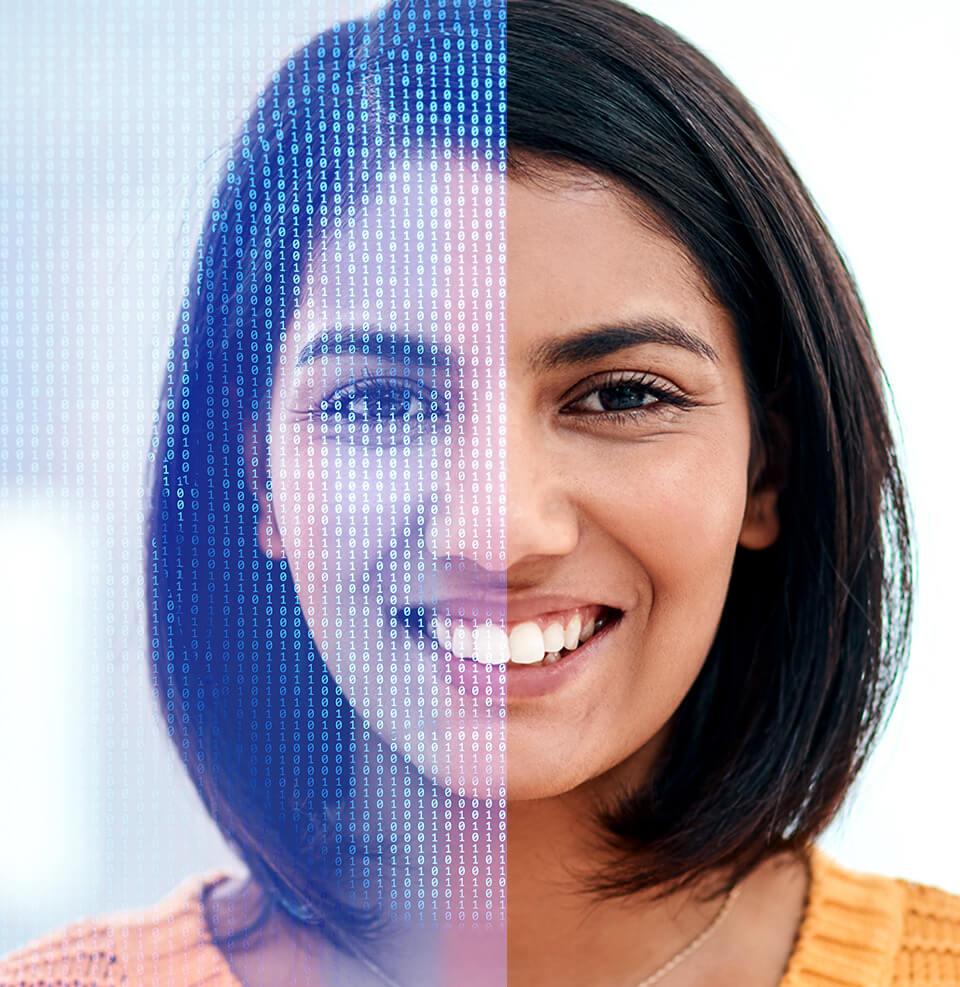
Biometric Authentication.
Confirm a person’s true identity with just a selfie. Fused with our proprietary image processing, our ID Photo-to-Selfie verification has the lowest processing bias in the industry.
With this simple, user-friendly way to authenticate an individual, you can match a person to the photo on a government-issued ID, profile pictures, or any other image of a person’s face with complete accuracy. Our liveness detection and face match detection ensure the person is actually present instead of a deepfake or spoof.
What makes our Biometric Authentication superior?
Our Biometric Authentication is powered by an unrivaled combination of Liveness Detection and Face Match technology. Here’s how it works.
Liveness Detection.
Liveness, spoof detection technology ensures the person taking a selfie is doing so in real-time. Ultimate detection is achieved using a robust combination of active and passive fused algorithms.
Face Match.
With Face Match you can ensure that the person in possession of a government-issued ID is the same person that matches the ID. Face Match’s facial recognition technology can be matched to other selfie images, profile pictures, or other previously captured database images.
Fraud Shield.
Power up a nearly impenetrable barrier against fraud. Fraud Shield, our proprietary biometric and biographic watchlist service, can almost instantly protect your company in real-time against even the most intensely rapid, prolific, inventive bad actors.
This “superpower” technology goes far beyond Identity Proofing to stop even more fraud vectors using our fused biographic and biometric watchlists to stop fraudsters and bad actors.
With AuthenticID Fraud Shield you can:
Flag and add fraudsters to a Bad Actors Watchlist
Stop mule activity and 1st party fraud
Track frequency of account creation attempts with our Velocity feature

Identity Decisioning Engine.
Our Identity Decisioning Engine simplifies data management for your teams and also functions as an identity orchestration layer for fused decision-making. It can be used in corroboration with third-party partner services when warranted by specific use cases.