Identity orchestration is the framework that businesses can use to weave a variety of identities together in a multi-cloud environment. Identity Orchestration allows businesses to enable consistent identity and access to a business’s apps and/or services, regardless of which identity system is used. Identity orchestration requires dynamic user journeys for IAM across the entire identity lifecycle, including fraud detection, identity proofing, and identity authentication.
Identity Orchestration Defined
Identity Orchestration solutions give organizations a unified view of all identities and their associated access privileges. This type of framework allows organizations to manage access across all systems and applications in a synchronized way–from one central location.
An Identity Orchestration framework is a crucial aspect of modern IAM strategies, especially as organizations increasingly adopt cloud-based and hybrid IT environments that require secure and efficient management of identities and access across a range of systems and platforms.
What is Identity Orchestration?
Identity Orchestration is a framework that businesses can use to weave a variety of identities together in a multi-cloud environment. It refers to the process of managing and coordinating various aspects of identity across multiple systems, applications, and platforms within an organization.
This type of approach allows businesses to maintain a consistent identity and access to a business’s apps or services, regardless of which identity system is used.
Identity Orchestration relies on dynamic user journeys for Identity Access Management (IAM) across the entire identity lifecycle, including fraud detection, identity proofing, and identity authentication.
When done correctly, Identity Orchestration can help organizations offer a seamless experience for users, while still maintaining comprehensive access control over their network.
How is Identity Orchestration Used?
In general, any organization that needs to manage user identities and access across multiple systems and applications can benefit from using an Identity Orchestration solution.
Identity Orchestration has become particularly useful in modern-day cloud-based and hybrid work environments as an efficient way for organizations to manage identities across multiple platforms, apps, and locations.
Since it is flexible and adaptable, Identity Orchestration allows organizations to create and manage dynamic user journeys for identity and access management throughout the whole identity lifecycle.
With this in mind, Identity Orchestration can be used in the following ways:
- Single Sign-On (SSO): users can log in to multiple systems and applications with just one set of log in credentials; this means they don’t have to remember multiple usernames or passwords, and can help prevent security breaches
- Access Control: organizations can easily define and enforce their access policies across their network; this ensures users can access the resources required to complete their tasks or duties while reducing the risk of unauthorized access
- Compliance Management: organizations can better comply with regulatory requirements when Identity Orchestration is in play because they have a centralized system for managing user access and monitoring their activity across the network; this simplifies the audit process, and reduces the risk of compliance violations
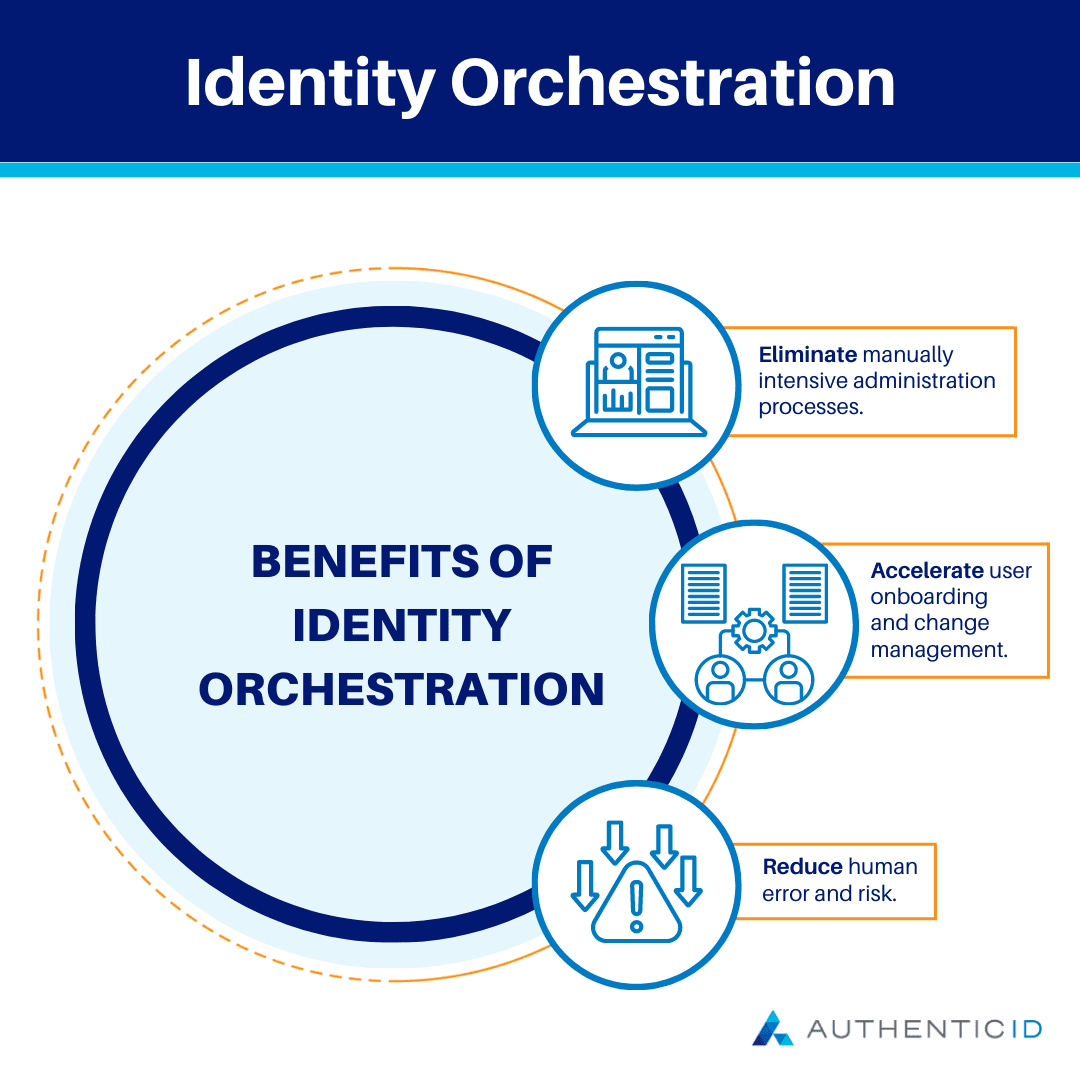
Benefits of Identity Orchestration
There are a number of reasons why organizations can benefit from Identity Orchestration, including the following list of potential advantages.
– Enhanced Security
Identity Orchestration helps organizations have more control over the access to sensitive data and systems within their network. Plus, organization administrators can monitor users’ activity across the network, allowing them to detect and address breaches more quickly.
Because of this, they can put themselves at less of a risk for a costly data breach or other security incident that occurs due to weak passwords, unauthorized access, or other security vulnerabilities.
– Better Efficiency
Additionally, organizations that implement Identity Orchestration solutions can get a centralized view of all identities and their associated privileges within their systems.
Identity Orchestration helps to streamline the management of access across multiple systems and applications, reducing the time and effort required to manage access manually. Even in an environment that’s becoming increasingly more complex, Identity Orchestration is the tool to make access management more simplified.
– Easier Compliance
An Identity Orchestration solution helps organizations achieve and maintain compliance and regulations such as GDPR, HIPAA, and PCI DSS.
By providing centralized visibility into user access across all systems and applications, Identity Orchestration helps organizations avoid compliance infractions, and makes the audit process much more straightforward and transparent.
– Scalability
As organizations grow and adopt new systems and applications, Identity Orchestration solutions grow with you to ensure that access management remains scalable and efficient, without additional manual effort required.
– Flexibility
Identity Orchestration solutions also support a range of authentication and authorization frameworks.
So, this helps organizations choose the methods and approaches that work best for their environment to successfully integrate with a variety of systems and platforms.
– Seamless User Experience
Users can also benefit from a more seamless and intuitive registration and login process when an organization uses Identity Orchestration.
These solutions can help remove some of the friction that users have traditionally faced throughout the identification and authentication process like providing proof of identity, verifying contact information, autofill forms for billing information, and more.
Plus, with just one set of login credentials to manage, users can be more productive by spending less time on login and registration.
Identity Orchestration Use Cases
There are many real-world applications of Identity Orchestration today, with the potential use cases only expanding as digitization efforts become more widespread across different industries.
Here are some examples of how Identity Orchestration can be used in practice:
• Healthcare: healthcare facilities and institutions can better manage user access to electronic health records and other sensitive patient data, in addition to helping them meet HIPAA requirements
• Education: educational institutions can manage user access to learning management systems and other educational applications containing student information; like in healthcare, a centralized identity management system helps educational institutions control account privileges and access to prevent sensitive student data from being accessed by unauthorized parties
• Finance: financial institutions can use Identity Orchestration to effectively manage user access to bank accounts, trading platforms, financial data warehouses, and other financial applications, protecting sensitive financial data that may be stored in these programs or systems
• Government: government agencies can manage user access to their systems and applications, including the protection of classified or top secret information, as well as managing access to government facilities; Identity Orchestration helps these agencies keep control over who can access their information and resources, and when
• Retail: retailers can use Identity Orchestration to manage user access to retail systems and applications like point-of-sale systems and customer loyalty programs so only authorized users can access sensitive customer data and financial information