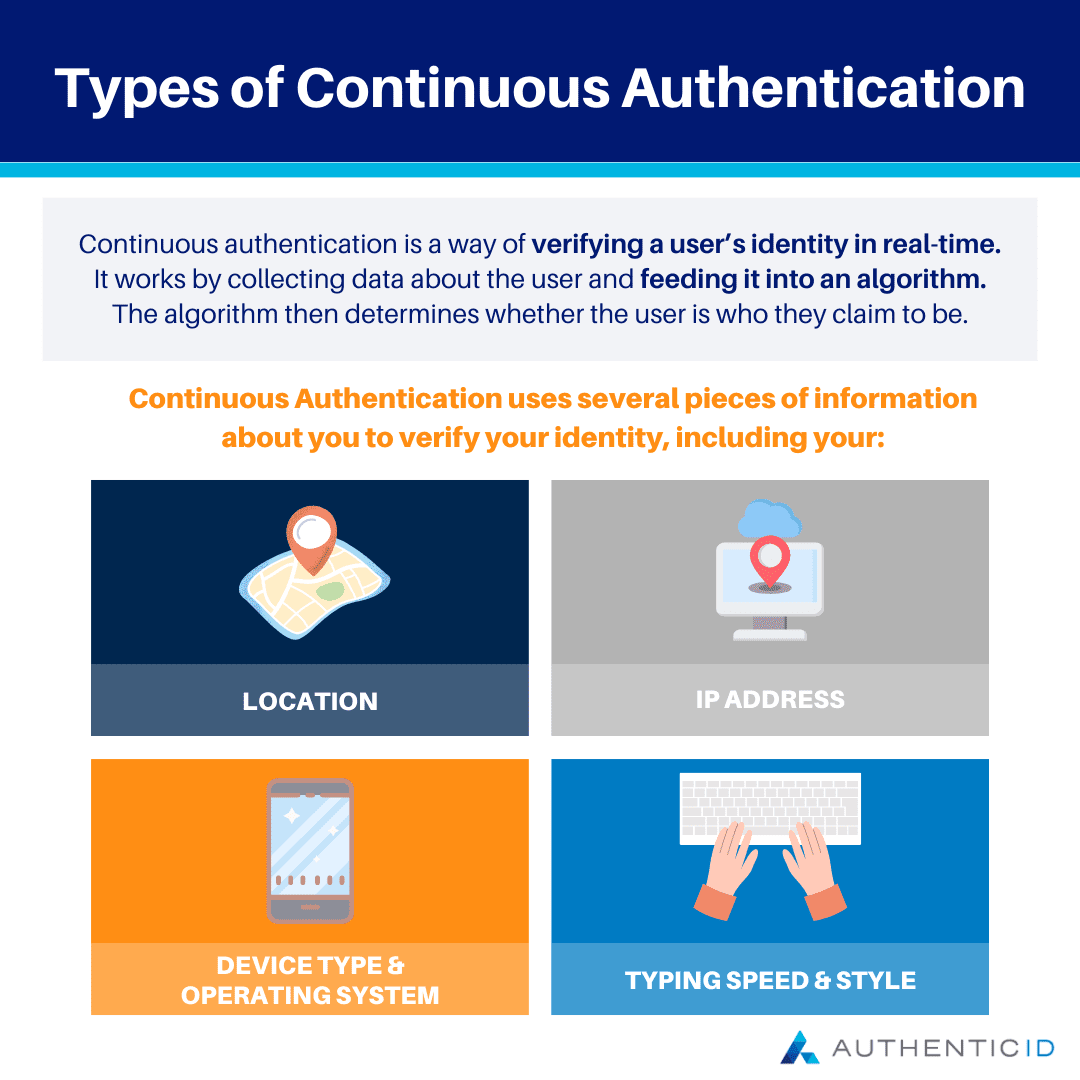
Continuous authentication is a way of verifying a user’s identity in real-time. It works by collecting data about the user and feeding it into an algorithm. The algorithm then determines whether the user is who they claim to be.
With standard authentication, users enter some credentials (such as their username and password) when they begin a session. They are then authenticated and granted access to whatever resource they are trying to access.
Continuous authentication is different in that it can verify many times throughout a session that the user attempting to access the system is who they say they are. This can be particularly helpful in cases where there is concern over identity theft or situations where there may be an attempt to steal sensitive data.
When you log in to your account with Continuous Authentication, we use several pieces of information about you to verify your identity, including your:
- Location
- IP address
- Device type and operating system
- Typing speed and style
How does continuous authentication work?
Websites, apps, and even smart home devices are constantly collecting information about you. This data is used to understand your behavior and create a profile around it. By using this profile, continuous authentication systems can determine whether you are who you claim to be or not.
What does continuous authentication collect data on?
Continuous authentication systems use any sensor that can collect data on its environment. These sensors include: Accelerometers, gyro meters, microphones, cameras, battery sensors, etc.
What kinds of things can you extract from this data?
In short: Everything! Your habits, routine, preferences, speech patterns, style of writing, and so much more.
Relevant industries and use case examples
Continuous authentication is a must for any industry, but it’s imperative in businesses that deal with sensitive information and where access to company systems is a privilege.
For example, many hospitals use continuous authentication systems to ensure that only authorized personnel have access to patient information. It’s also prevalent in the financial sector, where businesses need to protect customer data while still allowing employees to do their jobs.
Continuous authentication is gaining popularity in the manufacturing industry as more and more companies are relying on digital technologies to improve their processes.
Other industries include:
- Banking, Financial Services
- Government, Defense
- Education
- Entertainment
Regardless of what kind of information you’re protecting, continuous authentication can help you ensure that only authorized users have access to your company’s resources.
Continuous authentication is a feature that has become increasingly common in the technology sector, especially in security. Because it is such a new technology, many use cases continue to be discovered and explored. Here are just a few:
- In-home security systems. Many organizations use continuous authentication to verify that the person opening their front door is the homeowner or someone who has been given access to the home.
- Mobile banking apps. These apps often have continuous authentication features designed to keep users’ financial information safe and secure even when they aren’t using the app.
- Workstation logins. Some businesses require employees to log into their workstations every time they leave their desks—even if they are only going for a few minutes at a time—and some of these businesses use continuous authentication software as part of this process.
What are the advantages and benefits for using Continuous Authentication?
The first benefit of continuous authentication is that it’s always on. This means that you’re always authenticated (or authenticated-ish). This is a big deal because whenever your computer or laptop wakes up from sleep, you don’t have to log in again—you pick up where you left off. This can be especially helpful for people who use the same laptop for work and personal stuff—you don’t have to switch between accounts, and when you close your laptop to run out of the office, you don’t have to make sure all your work apps are locked before you do.
The second benefit of continuous authentication is that it’s very convenient. If you’re not on a work computer or laptop, you’re almost always logged into your stuff: Google docs, Facebook, Netflix, and whatever else you use.
Lastly, continuous authentication makes life harder for hackers. When someone tries to hack into your account, they’ll have to first hack into all the other accounts on your computer or laptop—which can either be very difficult or impossible depending on how vigilant all those account owners are (and how much sensitive data there is in their accounts for hackers to find and use).
In addition, Continuous authentication will help companies provide an incredible user experience for customers like never before. Customers need to feel confident in their privacy and the safety of their data, and this technology helps them do that—while still letting them move quickly and easily through their day-to-day activities.
What are some of the latest continuous authentication methods/technology?
Businesses are using continuous authentication methods to keep their data secure.
Recently, a new wave of continuous authentication methods has been developed. Two of the most promising are “continuous liveness detection” and behavioral biometrics. Both rely on machine learning and are harder for hackers to spoof or bypass.
Continuous liveness detection is a two-part process that requires users to interact with their devices to demonstrate their presence. Users can be asked to move the device, tap it, swipe it, or even make faces at it.
What are other new methods used in continuous authentication? Behavioral biometrics.
Behavioral biometrics, also known as behavioral analytics, analyzes how users interact with their devices to determine whether or not they are who they claim to be. This analysis typically involves examining how users type on their keyboards and tap on their touchscreens based on patterns that have been established during previous sessions.
Other common forms of behavioral biometrics include:
- Gait analysis (how a person walks).
- Keystroke dynamics (how a person types).
- Mouse movement (how a person moves their mouse).
In addition to these methods, behavioral biometrics can also include other “passive” factors such as geolocation data (where a user is located) and device data (what kind of device they’re using).