Cell phone usage in the United States has skyrocketed over the past decade, with 97% of people in the country owning this type of device. While cell phones have offered immense convenience and online access to users around the world, they also provide an easy avenue for fraudsters to gain access to your sensitive personal information for their own financial gain.
Specifically, cell phone users face the risk of SIM swap fraud, which can be difficult to resolve and come with devastating consequences for victims. For more information on SIM swapping and how to avoid this type of fraud, continue reading below.
What Is a SIM Card?
Before we dive deeper into SIM swapping, it’s important to understand what a SIM card is and why its security is so critical. SIM stands for subscriber entity module, which controls a person’s calling, texting, and data services. Each SIM has a unique identifier that is designated to a specific person.
In practice, this allows you to transfer your phone number, data, and personal information from one device to another when you upgrade your cell phone without having to start over from scratch. Or, if the SIM card gets lost, the information stored on the old one can be transferred to a new SIM card. This can be highly beneficial to actual cell phone users who have lost their devices unexpectedly. However, this can also be a vulnerability that allows for SIM swap attacks.
SIM Swapping Explained
SIM swapping, or a SIM hijacking attack, is when a fraudster has a victim’s phone service switched from their existing SIM card to one that they control. Typically, the purpose of doing so is to bypass multi-factor authentication (MFA) so they can gain access to the person’s bank account or other sensitive information.
How It Works
To complete a SIM swap, the hacker requires the victim’s credentials or personal information, which they may have obtained through purchasing it on the dark web or through a phishing attack. Armed with this information, they will impersonate the victim and try to convince their cellular provider to swap their number to a SIM card that the fraudster has in their possession.
Once the transfer is complete, they can intercept all of the victim’s phone calls and text messages. All carrier-related services associated with the original SIM card will cease. With this, fraudsters will receive the one-time codes that are sent to an account holder’s cell phone number when trying to log into their bank account or other online service. In other words, a SIM swap helps criminals successfully bypass multi-factor authentication.
In turn, this may place a person’s bank account, social media accounts, text messages, and other sensitive information in the wrong hands. In some cases, the fraudster may even try to extort the rightful owner to purchase their number back from the hacker or sell the phone number to other criminals.
The SIM Swapping Problem in Telecommunications
The FBI estimates that in 2022, $72 million was stolen from victims through SIM swap attacks, a meaningful increase from the amount lost in 2021, which was $68 million.
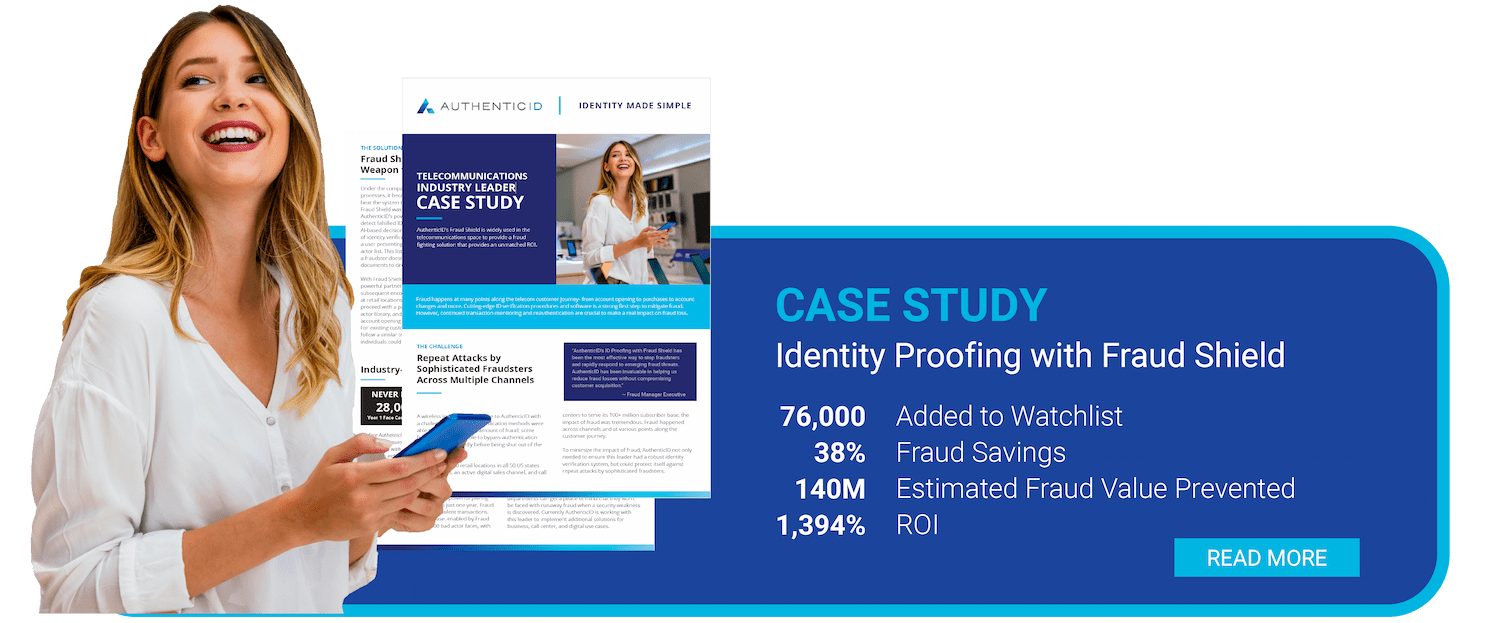
The rising prevalence of SIM swapping incidents underscores the need for more robust identity proofing processes and enhanced security measures in the telecommunications industry. Luckily, providers are beginning to implement stronger authentication protocols, like biometric verification, to help improve security before users can change their SIM cards to protect their customers from fraud.
How Users Can Detect a SIM Swap Attack
If you do fall victim, there are some obvious signs that might hint a SIM swap attack is underway so you can intervene quickly. This includes:
- Unusual alerts from cellular service providers: Users may receive unexpected alerts from their providers about changes to their service when the fraudster is trying to swap the SIM card
- No cell phone service: Users notice they have suddenly lost cell service and are not able to access cellular data, make phone calls, or send text messages, reflecting that their SIM card has been deactivated
- Unauthorized banking activity: If a user is locked out and unable to access their bank account, or they notice unauthorized transactions, it may signify a SIM swap attack has taken place
- Strange social media activity: There may be strange posts placed on the user’s social media profiles, or messages sent to their friends and followers that they do not recognize
How Users Can Prevent a SIM Hijacking Attack
SIM swapping is a growing concern for consumers, though there are ways to combat the issue and keep yourself protected. Above all, focus on keeping your personal information safeguarded, which will make you less vulnerable to this type of fraud.
Follow Password Best Practices
Use passwords that are strong and unique, and avoid reusing passwords across multiple accounts and devices. This way, if one of your passwords is compromised, the rest of your accounts will remain secure. Regularly change your passwords, especially when prompted by a service provider.
Be Wary of Unexpected Communications
If you receive a text, email, or call from someone you don’t recognize, safeguard your personal information and avoid handing over any sensitive data until you’ve confirmed the legitimacy of the person’s request with your cellular service provider.
Especially if the person on the other end is urging you to act quickly, take a step back and consider any potential warning signs. This is a common tactic among fraudsters to play on your emotions and keep you from thinking critically. If you receive a suspicious message from someone claiming to be your provider, alert them of the issue right away.
Stay Informed
As technology advances, fraudsters’ techniques continue to advance and become more sophisticated. To keep yourself secure, it’s important to stay educated on the latest security threats and techniques. It will help you build awareness and be better able to prevent and detect a SIM swap attack.
How Businesses Can Prevent a SIM Hijacking Attack
SIM swapping is a growing concern for consumers, and businesses can play a role in preventing SIM swaps. A layered security approach can offer organizations a stronger barrier against SIM swapping and SIM hijacking attacks.
One tool businesses can use in their standard security practices is biometric authentication. When paired with ID verification of a government-issued identity document, businesses can ensure users are who they say they are.
In addition, businesses can use reauthentication to further prevent unauthorized user access during an active login session when SIM card transfer is requested, offering another, higher level of security by asking a number owner to verify their identity with biometrics.
The rising threat of SIM swapping can be countered by both consumers and businesses by using robust security measures, using advanced technology like biometric authentication, as well as consumer and employee best practices education. Businesses must stay ahead of SIM swap and other fraud attempt vectors as bad actors make new, sophisticated attempts to obtain personal information.
Prevent SIM Swapping and SIM Hijacking Attacks
You can protect your customers against SIM swap fraud by leveraging biometric authentication to assist call centers and other frontline employees to identify and stop fraudulent requests. With identity verification, telecommunications companies can accelerate customer checkout, decrease customer abandonment, and prevent fraudulent chargebacks. Request a demo or contact us to learn more today.
